An IP spoofing is a hacker uses some tools to modify the source address in the packet header to make the receiving system or device think the packet is from a trusted source, such as another computer on a local network, and accept it. Here comes two methods to prevent such spoofing events from WAN or LAN site:
- Setup on Web UI (On firmware version 3.8.8 or later)
- Telnet commend (On firmware version 3.8.7 or older)
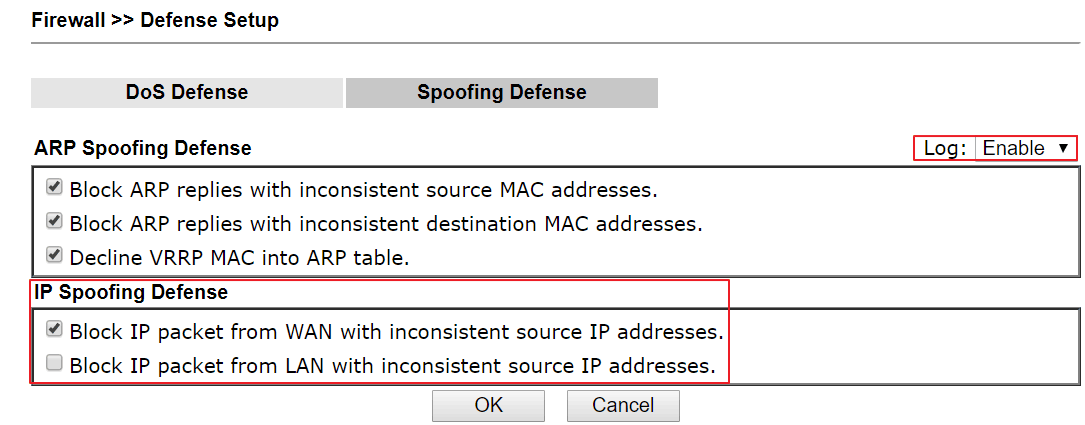
Setup on Web UI (On firmware version 3.8.8 or later)
Go to Firewall >>Defense Setup >> Spoofing Defense page.
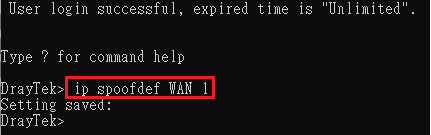
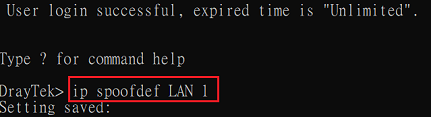
Telnet commend (On firmware version 3.8.7 or older)
1. Telnet into Vigor Route
2. Enter command,
- To enable Block IP packet from WAN with inconsistent source IP addresses, enter “ip spoofdef
WAN 1”, and it will return “Setting saved:”
- To enable Block IP packet from LAN with inconsistent source IP addresses, enter “ip spoofdef
LAN 1”, and it will return “Setting saved:”
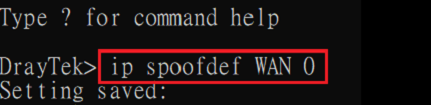
Note:
- To disable Block IP packet from WAN with inconsistent source IP addresses, enter “ip
spoofdef WAN 0”.
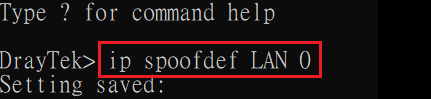
- To disable Block IP packet from LAN with inconsistent source IP addresses, enter “ip
spoofdef LAN 0”.
There are two options:
1. Block IP packet from WAN with inconsistent source IP addresses (Enabled by default)
While receiving packets from WAN, Vigor Router will check if the source IP address and the coming WAN interface is reasonable. If not, Vigor will drop the packet instead of forwarding it to the internal server.
For example, if Vigor’s LAN network IP address is 192.168.1.1 and it receives the packet from WAN with the source IP
192.168.1.100, Vigor will drop the packet and send the defense log like the follows:
[IP Spoofing Defense]Block packet from WAN with source IP: 192.168.1.100
2. Block IP packet from LAN with inconsistent source IP addresses
When receiving packets from LAN and the option is enabled, Vigor Router will check if the source IP and the coming LAN
interface is reasonable. If not, Vigor will drop the packet and display the log
below:[IP Spoofing Defense]Block packet from LAN with source IP: 192.168.239.31
Published On:2020-11-13
ShareWas this helpful?
