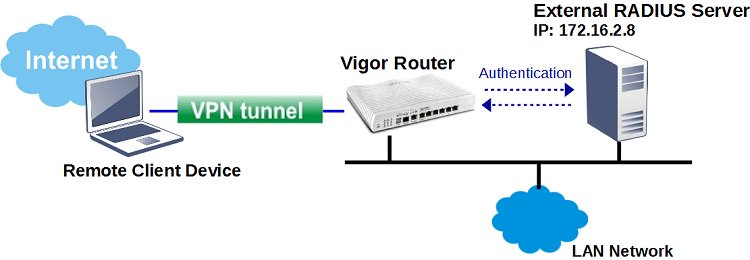
If you already have a RADIUS server on your network, instead of using the router's local user database, you may also authenticate the Remote Dial-In PPTP/L2TP/SSL/OpenVPN VPN clients by the external server. This article explains how to configure Vigor Router to use an external RADIUS server for VPN authentication.
1. Configure the RADIUS Server settings in Applications >> RADIUS/ TACACS+.
- Enable External RADIUS
- Input Server IP Address as the IP address of RADIUS server
- Input Share Secret of the RADIUS server
- Confirm Share Secret
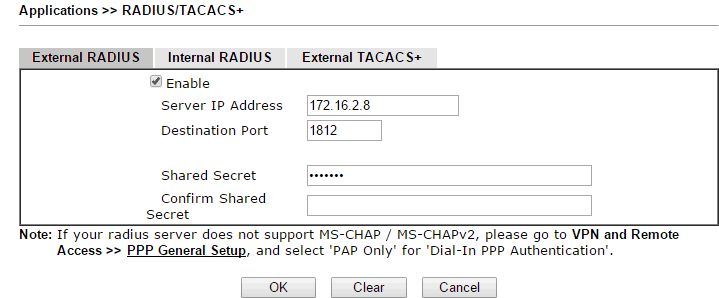
2. Click OK to apply. Vigor will request a system restart.
3. Configure the router to authenticate Remote Dial-In VPN clients with an external server: Go to VPN and Remote Access >> PPP General Setup, and enable “RADIUS” in PPP Authentication Method.
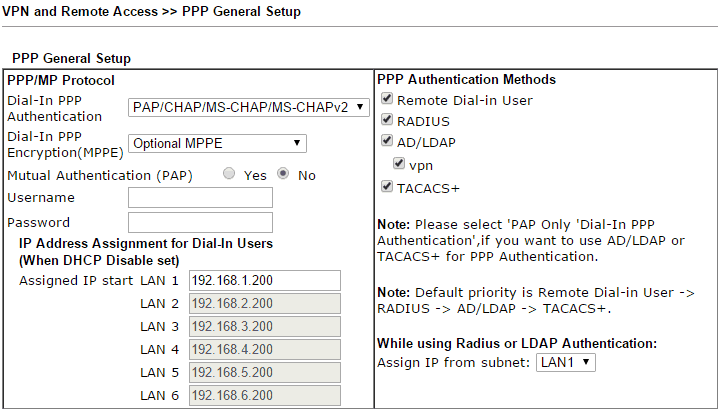
Note: There are 4 PPP Authentication Methods: Remote Dial-In User (the local database), RADIUS, AD/ LDAP, TACACS+. When all of them are enabled upon an authentication request, Vigor Router will try the local VPN Remote Dial-In profiles first. If it does not match, the router will next forward the authentication information to the RADIUS server, and then to the LDAP/AD server, until the authentication fails.
4. With the above configuration, remote clients will be able to establish a VPN connection while login with the user accounts in RADIUS server.
Note: Vigor router also supports Frame-IP-Address from RADIUS server to assign an IP address to VPN client.
Troubleshooting:
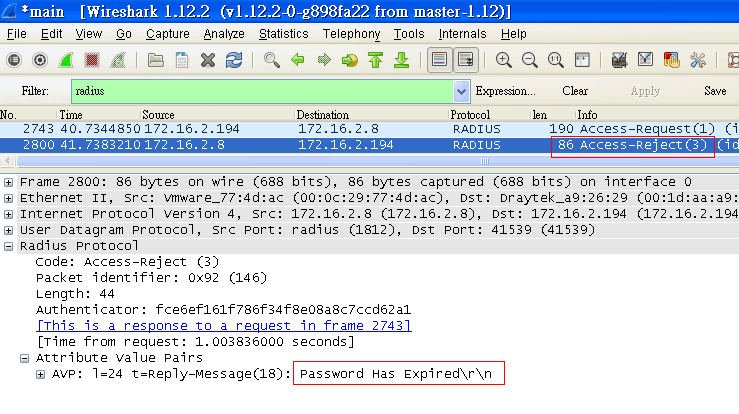
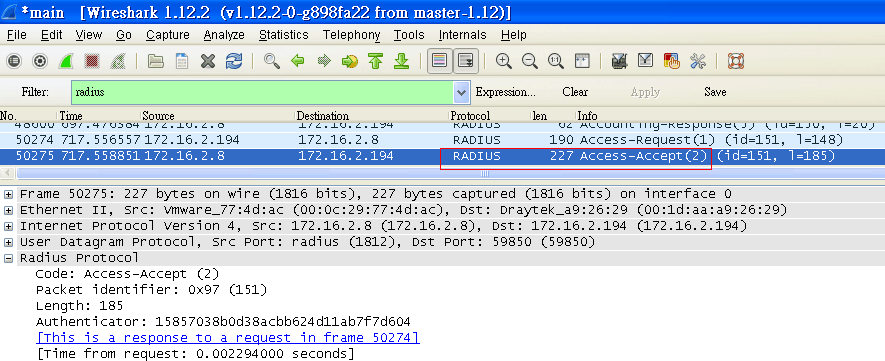
When VPN over RADIUS authentication failed, we can capture packets on the RADIUS Server by Wireshark to debug. And here are some common reasons:
- Password error or expired, If the server responds "Access-Reject", authentication fails may because of password error or the password has expired.
- Pre-shared key mismatch: If the server responds "Access-Accept", it may because Shared Secret is not matched. Please re-type Shared Secret on both Vigor Router and on the RADIUS server then have a try again.
Note: Vigor Router uses UTF-8 encoding, while Windows RADIUS server uses big5. Please prevent any special characters in Shared Secret with Windows RADIUS server.
If it still doesn't work, please e-mail the below information to [email protected] for us to debug: 1. Remote management info to Vigor Router 2.An account/ password on the RADIUS server for testing remotely
Published On:2015-05-12
Was this helpful?
