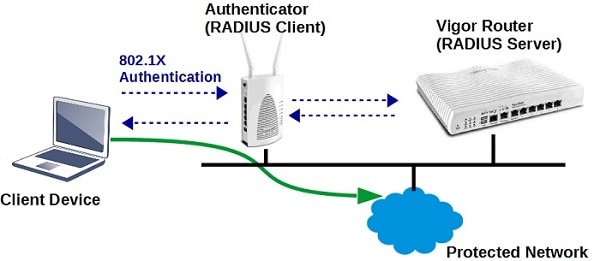
Selected Vigor Routers have built in an internal RADIUS server, and they can act as authentication servers for 802.1X authentication. This document introduces how to set up Vigor Router to be a RADIUS server.
1. Create user profiles: Go to User Management >> User profiles, click on an available profile index, enable this profile, enter Username and Password
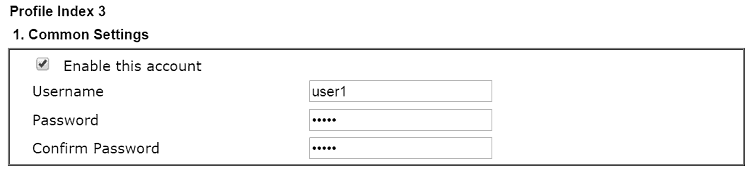
2. In Internal Services, enable RADIUS, so that this profile can be used for RADIUS clients. Then click OK to save.
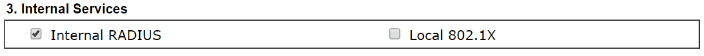
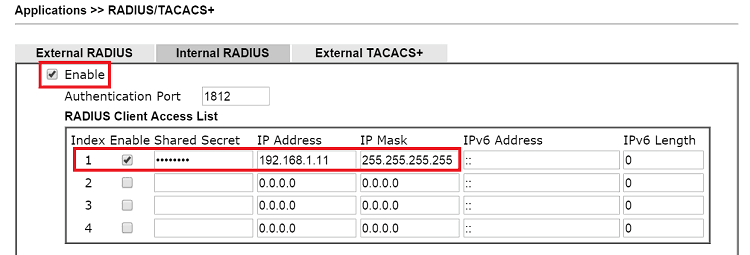
3. Enable internal RADIUS: Go to Applications >> RADIUS/TACACS+ >> Internal RADIUS page,
- Enable Internal RADIUS
- In RADIUS Client Access List, enable an index, enter Shared Secret, and enter the IP Address and Mask which is allowed to access Vigor Router as RADIUS client. (This step can be skipped if you are using the Internal RADIUS server for local 802.1X Authentication.)
Tips: If there are more than 4 RADIUS clients, please set a larger mask to apply to more RADIUS clients in the same subnet. - Click OK to save and reboot the router
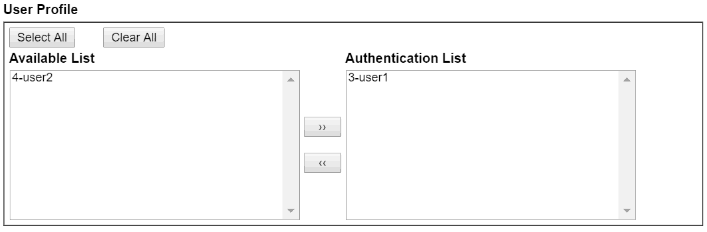
User Profile shows the user profiles stored on the router. The profiles in Authentication List are the profiles that have "RADIUS" enabled and can be used by RADIUS client, such as the profile created in step 1. The profiles in Available List are the user profiles that don't have "RADIUS" enabled; however, if you would like RADIUS client to use those profiles, you may select the available profiles and click on ">>" to put them into Authentication List.
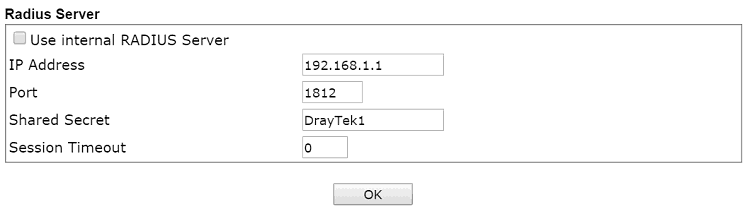
4. RADIUS client setup: For the 802.1X authenticator which would like to use Vigor Router as RADIUS server, need to enter the IP address of Vigor Router and Shared Secret set in step 2.
If you are using the Internal RADIUS server for local Wi-Fi authentication, select a security Mode that uses 802.1X at Wireless LAN >> Security, and click the link "Wireless LAN 802.1X Setting". In the Setting page, set Authentication Type as "Local 802.1X" and check "Enable", then click OK to save.

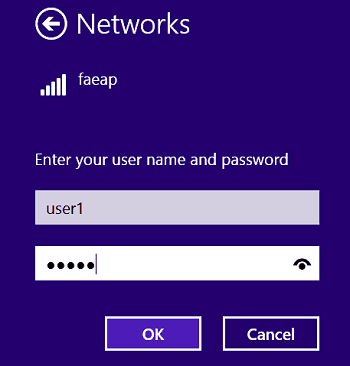
5. After the above configuration, when client devices connect to RADIUS client (the authenticator) and attempt to join the network, they will be asked to enter the credentials first, which should be the username and password set in step1.
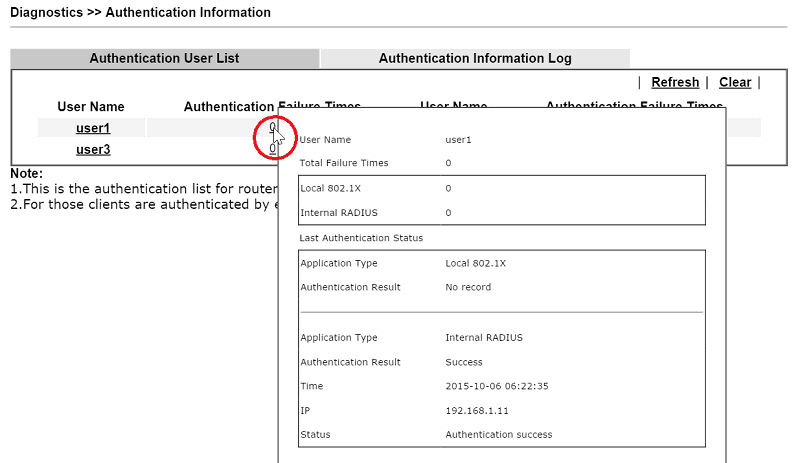
6. And from Diagnostics >> Authentication Information, the network administrator may check each user's last successful authentication and failed attempts.
Troubleshooting
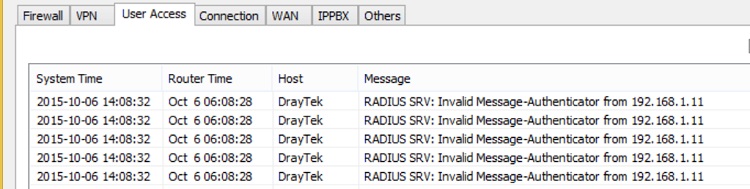
If the client devices failed to join the network, and the Syslog shows RADIUS SRV: Invalid Message- Authenticator from [Radius Client IP], it might because that the shared secret of client and server do not match.
Published On:2016-04-01
Was this helpful?
